Blockchain Byte - Week 23 : Block Mining
Table of Contents
- Recap
- Mining
- Validation Controls
- Nonce
- Target
- Game of Dice
- Summary
Recap
During week 22, we explained how blocks are "chained" to each other thus earning the name Blockchain.
We deep dived into block headers which contain the following fields :
- The previous block hash
- Fields related to mining
- Merkle Root Tree - a unique hash of all the transactions in the block combined.
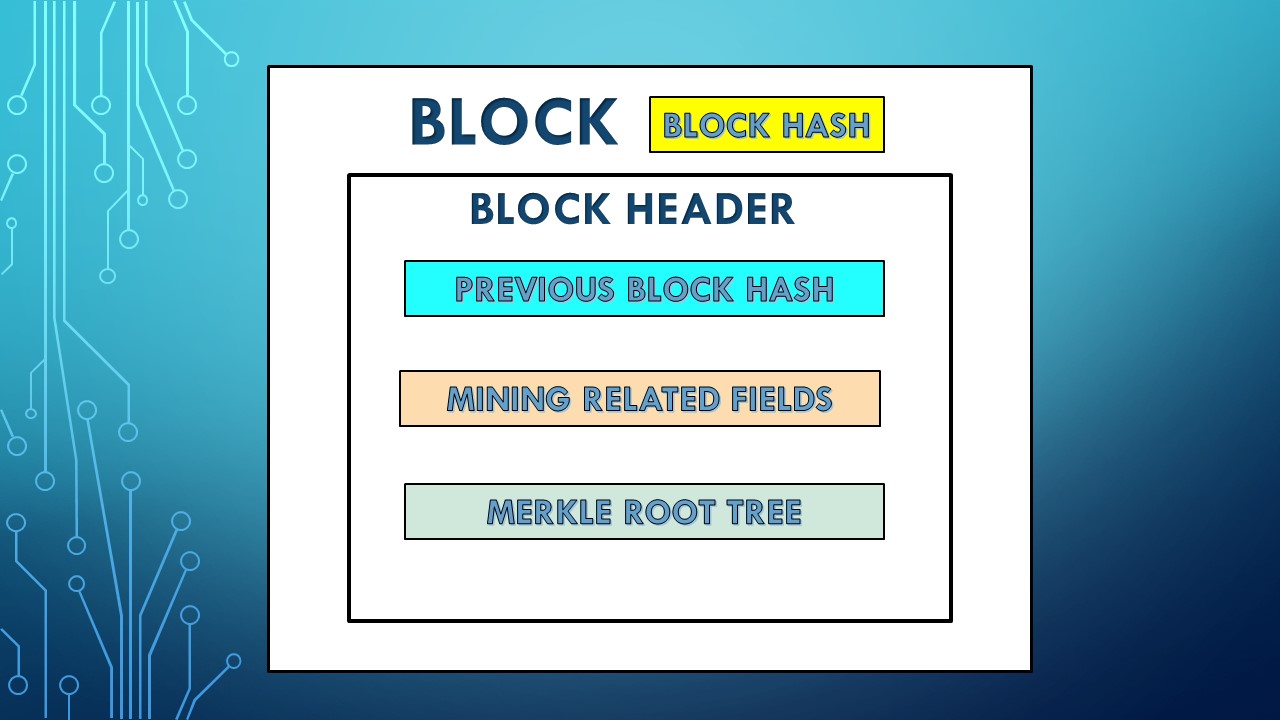
We explained the previous block hash during week 22. Before we get into fields related to mining, let us explain what exactly is mining in a blockchain?
Mining
Mining is the process of appending new blocks to the blockchain data structure
It is the mechanism by which transactions are authorized and added to the decentralized ledger. It's like adding a new tab with transactions to an excel file.
So, when a new block is added to the existing chain of blocks, we say the block is mined.

Let us go back to transaction authorization in a bank. There are system & organizational controls in place when inputting and authorizing transactions like :
- Only an authorized staff who has the relevant system privileges can input a transaction.
- A bank staff who has the system privileges to authorize a transaction only can do so and no one else.
Similarly, in a blockchain, only certain nodes can mine blocks. These nodes are called miner or mining nodes. Miner nodes VALIDATE transactions and ADD THEM to the decentralized ledger.
So, the next question is are there any controls when adding transactions to the decentralized ledger? Not in the traditional sense.
Validation Controls
In the absence of any controls like that in centralized systems, how is transaction integrity ensured in a decentralized ledger? This integrity is ensured by increasing the complexity & cost of mining a block that acts as a deterrent to add a fraudulent or false transaction to the ledger. What does this mean & what happens if a miner adds fraudulent or false transactions to a block?
We know that miners can add blocks to the blockchain. But these blocks have to be validated by the other nodes in the network & agreed by all of them to get confirmed (called CONSENSUS - Refer Week 9 & Week 10 for more details on consensus) . If there are fraudulent or double spending transactions, these will be rejected by the nodes thus rendering that block invalid.
Now, assume the miner spent significant resources like processing power and electricity to mine the block. Then, all that effort & cost of adding the block would go to waste. Also, the miner would lose incentives which they would've earned in the form of newly minted bitcoin & transaction fees (Refer Week 14 & Week 15 for more details on incentive mechanisms). Thus, there is a strong deterrence by way of high effort & cost to ensure miners add only valid transactions to the blocks.
A miner node can add blocks to a blockchain only after solving hard cryptographic puzzles. And these nodes compete with each other to add blocks to the blockchain. The puzzle is so difficult to solve that there are specialized hardware only to solve these puzzles. The cost factor to mine a block is the processing power and electricity expended for solving this problem.
The solution to the cryptographic problem is called PROOF OF WORK. What is this cryptographic problem and what is proof of work solution?
Let us now explain the two fields related to mining in the Block Header. These are
- Nonce
- Target
Nonce
During mining, the block header is hashed repeatedly, changing one parameter, till the resulting hash matches the specified target. The hash function SHA256 is used in the bitcoin mining process. Sounds a mouthful? Let us visualize it with an example below:
Go to this website sha256algorithm.com.
There is a place to input text on the top left where you can input any text and the SHA256 hash output will be displayed at the bottom. The below screenshots will help in visualizing the same :
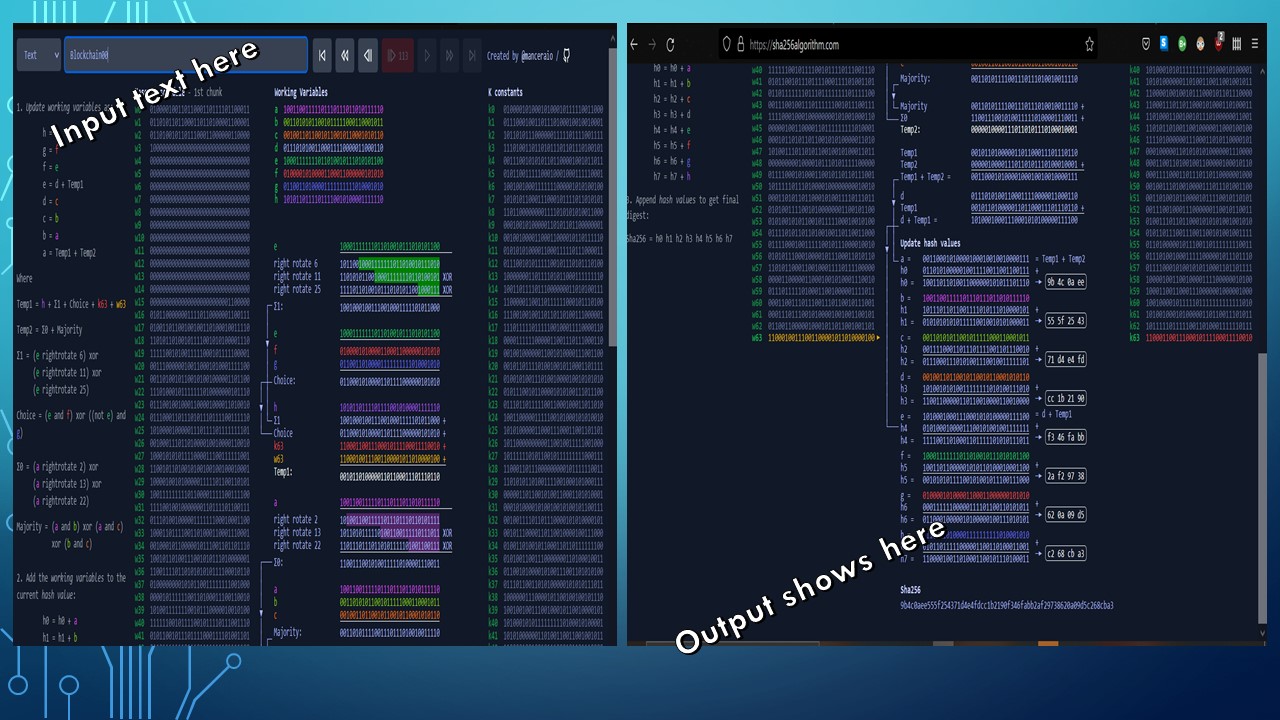
Now, let us do an exercise to hash through a block header called "Blockchain" and find out the SHA256 hash outputs. If we hash "Blockchain", we will get the same hash. To get different hashes, we need to add a parameter which will change each time we run the hash. So we add two digit numbers from 00 to 10 as below :
Blockchain00
Blockchain01
Blockchain02
Blockchain03
Blockchain04
Blockchain05
Blockchain06
Blockchain07
Blockchain08
Blockchain09
Blockchain10
The below is the SHA256 hash for each of the above items
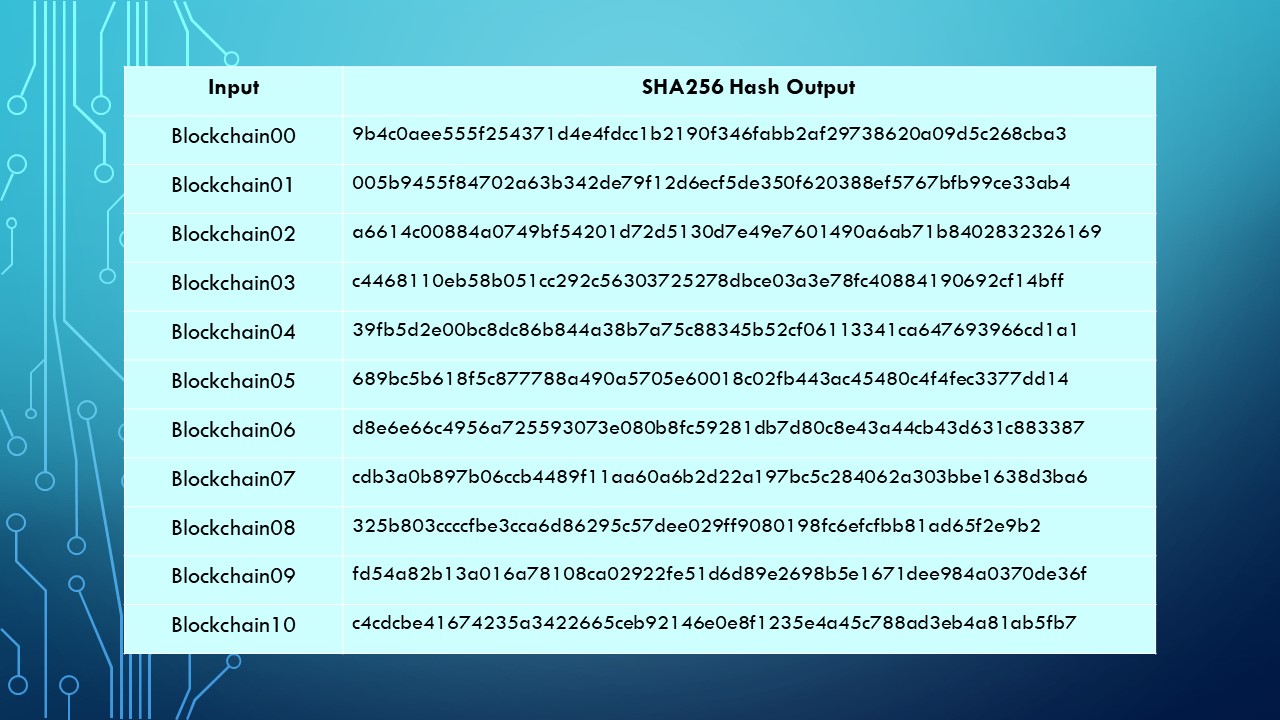
Each of the above produces a completely different hash even though the only difference in the input is the last two digits which starts from 00 to 10. The last two digits which vary in the above list is called a NONCE. The nonce is used to iterate through a series of inputs to produce a different set of hash outputs.
- Why do we have to do all this hashing and iterations ? and
- Why do we need a Nonce?
For answering the above questions, let us now understand what is target.
Target
The goal of all this hashing and iterations is to find a hash that is less than or equal to something called TARGET. In other words, the proof-of-work algorithm must produce a hash that is less than or equal to the target.
What is this target? Who fixes this target and how is it calculated?
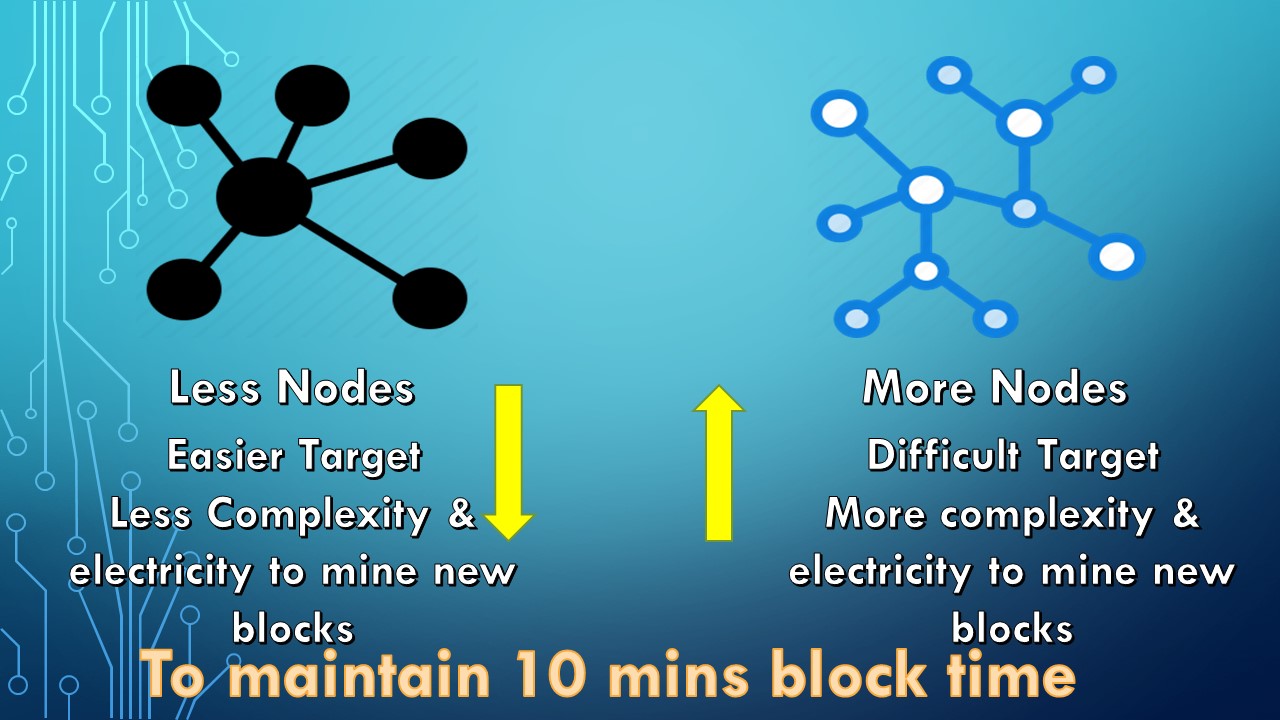
If we take Bitcoin Blockchain, blocks are generated every 10 minutes on an average. This is called Block Time. It refers to the time it takes to mine a new block. In Ethereum, the average block time is between 12 to 14 seconds. This expected block time is fixed by the protocol itself and adjusts itself taking into consideration the increase in nodes and processing power over the years. This means
- If the number of nodes or the processing power of the nodes increase which can result in more blocks being mined, the protocol adjusts the difficulty level (target) to make it more difficult to mine the block - meaning more processing power & electricity or
- If the number of nodes decrease or there is a decrease in processing power, the protocol adjusts the difficulty level (target) to make it easier to mine the block - meaning less processing power & electricity.
Thus, the 10 minute block time is kept constant across irrespective of the number of nodes or increase in processing power.
The below visualization makes it clear to understand
Now, what do we exactly mean by
- finding a hash that is less than or equal to the target
- How does the protocol make it more or less difficult
Game of Dice
Let us play a numbers game with a pair of dice

Photo by Brett Jordan on Unsplash
Assume in this game we are given a target and we have to throw a pair of dice equal to or less than the target over several rounds.
In the first round, our target is to get a number less than or equal to 10. Unless we throw 6+6, or 5+6, we won the first round and we don't have to throw much to arrive at the target.
In the second round, our target is to get a number less than or equal to 9. Unless we throw 6+6 or 5+6 or 5+5 or 4+6, we won the second round and we have to throw slightly more to arrive at 9 compared to 10
Assume after several rounds, the target is down to 3. Now, the number of throws required to get a number less than or equal to 3 will increase exponentially meaning it gets tougher to arrive at 3 and we will have to keep trying again and again till the pair of dice gives us a combination of 3 or less.
The below visualization makes it more easy :
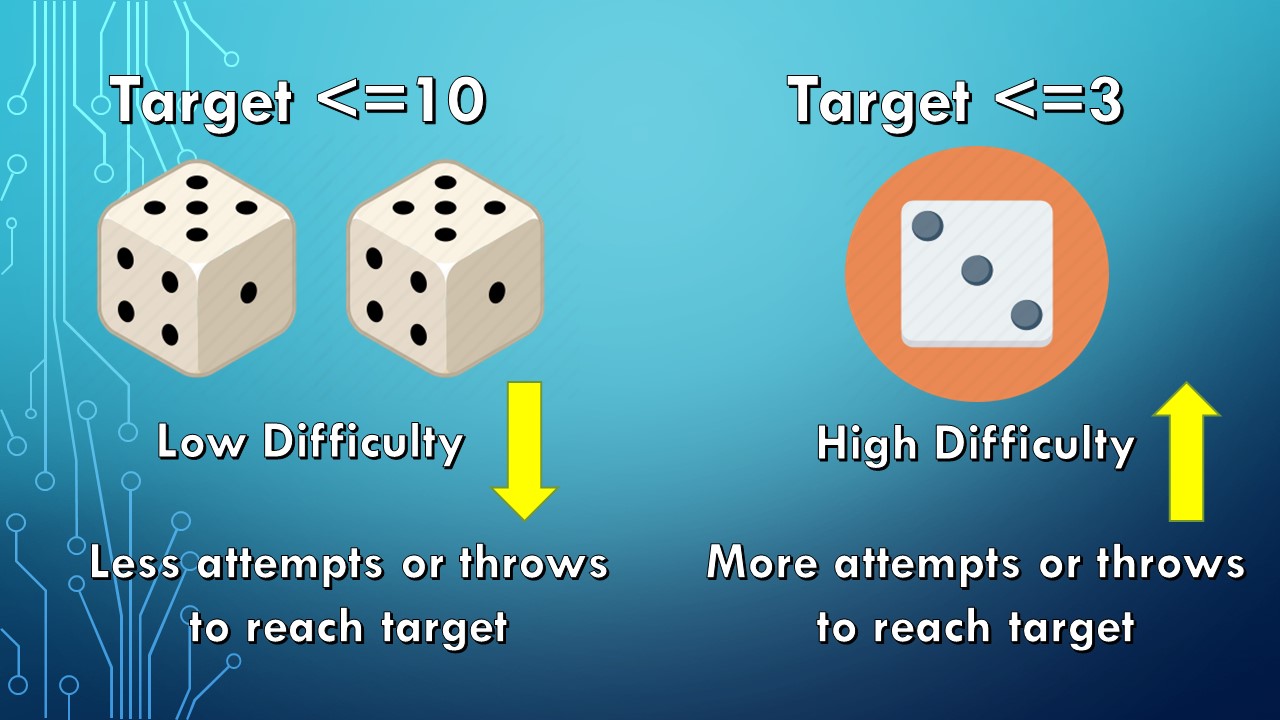
Using the above analogy, the target hash
- Is set at a lower threshold when the difficulty level should be higher and
- Is set at a higher level when the difficulty level should be lower
In place of throws, it is the number of hashes which needs to be done to arrive at the target.
For example, to make it more easier to mine a block, the target hash would be set at say, 10 and hence lesser number of hashing attempts would be required to get a hash equal to or less than 10.
To make it more difficult to mine a block, the target hash would be set at say 3 and more number of hashing attempts would be required to get a hash equal to or less than 3.
Now, one question. When we throw dices, different numbers show up making each attempt unique. If we hash the same block header every time, it will throw the same hash at every attempt. For example, if we hash the word "Blockchain", we will get the same hash every time. So, we need a field which will iterate or change each time we run a hash. Thus, in our example above, we added numbers 00 to 10 after the word "Blockchain" (called NONCE) to iterate each time so that one of those iterations will make the hash less than the target.
In our example above, let us assume that the target requires us to get a hash which starts with two zeroes. This is achieved in "Blockchain01" meaning it took one attempt for us to achieve that target. This is where a nonce changes like a counter each time incrementing by n to change the block header so that the required target hash is arrived say at X attempts.
Summary
To summarize :
- Mining is the mechanism by which transactions are authorized & added to the decentralized ledger.
- Mining can only be done by specialized nodes with specialized mining rigs called MINER NODES.
- Miners spend resources like processing power & electricity to mine a block.
- The processing power & electricity is used to solve a problem whose solution is called PROOF OF WORK
- The objective of solving the problem is to arrive at a block hash which satisfies a target condition.
- The complexity of the problem is controlled by the protocol depending on the number of nodes & their processing power. More number of nodes mean higher difficulty threshold & lower number of nodes mean lower difficulty threshold.
- The target field in the block header gives the target which the miner has to solve for them to add the block to the blockchain
- The Nonce field is used to iterate the block header to keep hashing till the output hash satisfies the target conditions
Now that the miner solved the proof of work, what next?